"With blockchain analytics the thing we say over and over is that all this activity is on this ledger forever, and if you did something bad 10 years ago you can be caught and arrested for it today. The fact that they're pulling up those transactions is really significant." – Sarah Meiklejohn, as quoted by Wired
Crypto is an endless source of fascinating material for Doomberg. I freely admit I didn’t know all that much about crypto before starting this journey – still don’t, really – but deep domain knowledge isn’t always necessary to ascertain the big picture and to have fun climbing the learning curve. Besides, I assume most readers of this Substack aren’t deep crypto experts either and are happy to come along for the ride.
I should also clarify that I’m not personally pro- or anti-crypto per se. My fascination with the topic comes from the incredible amount of utterly blatant lawlessness that seems so easy to spot by anybody curious enough to look. As a person who tries hard to follow the rules and operate within the confines of the physical society of the here and now, I am flabbergasted by the risks certain key crypto players are willing to take in the hopes of achieving the digital riches of tomorrow. This is even more shocking when one considers the permanency and public nature of blockchain ledgers.
A regular retort from crypto enthusiasts goes something like this: the US dollar is a giant Ponzi scheme, Wall Street is totally corrupt and exists to enrich the top 1%, the big banks launder billions of fiat currency per year for all manner of unseemly characters, and our politicians are nothing more than a mob family with unjustified power to police us. To which I say I totally agree!!! I simply marvel at the naive belief – held by most people in the crypto space – that the powers that be either don’t have the ability to beat down this rebellion or somehow will be unwilling to do so at the time of their choosing.
That time appears to be pretty much now.
This week’s crypto adventure begins with the infamous Poly Network hack, in which somebody with much more programming talent than this chicken pilfered $613 million worth of various digital tokens, only to eventually give it back. It was the biggest decentralized finance (DeFi) hack of all-time, far exceeding the total cumulative DeFi hacks for 2021. Why did the hacker(s) give it back? They claim this was their intent all along, although the blockchain record hints at an alternative explanation: laundering crypto at that scale is really hard if everybody is looking.
As mentioned earlier, the blockchain ledgers are permanent and public, something Poly Network was quick to take advantage of. Shortly after the hack, they published the hacker’s wallet addresses on Twitter, calling on the leading exchanges to blacklist those addresses in an effort to contain the damage and preserve the possibility of recovery.
The tactic worked! The hacker was stuck with the digital equivalent of an 18-wheeler’s worth of stolen Rolex watches with widely known serial numbers that no pawn shop would accept. Score a big win for crypto, right? In some important ways, absolutely, although the hacker could have squatted on that $613 million forever. They could have given it away as charity to various random wallets. They could have patiently tried to launder it ever-so-slowly over years. Poly Network might have prevented the hacker(s) from immediately benefiting from their theft, but clearly the whim of the hacker(s) is all that stood between Poly Network’s potential salvation and total devastation.
I knew I had to write about this situation, but I wasn’t sure which direction I’d go until I was watching my new favorite YouTuber’s take. Coffeezilla – a channel we’ve discussed before in the context of the Save the Kids rug pull – had his typically excellent and entertaining take on the event, but something he mentioned almost as a throw-away line really caught my attention. He detailed some of the messages the hacker(s) sent while deciding what to do with the bounty, including a reference to an Ethereum mixer called Tornado Cash:
“WONDER WHY TORNADO? WILL MINER STOP ME? TEACH ME PLZ!”
A crypto mixer?! I had a vague understanding of what crypto mixers were (they literally exist to anonymize crypto holdings, thereby facilitating money laundering), but I assumed they were illegal and banished as taboo by most of the crypto universe. Coffeezilla made the point that the mere mention of Tornado showed an intent on the part of the hacker(s) to capture at least some of their ill-gotten gains. For me, the concept that crypto mixers were still a thing was a mild surprise. Thus began my journey into the world of crypto mixers and the discovery of what I think is a critically important and quite recent precedent set by the DOJ. I believe it flashes a giant red “danger” sign for the crypto world for the months and years to come.
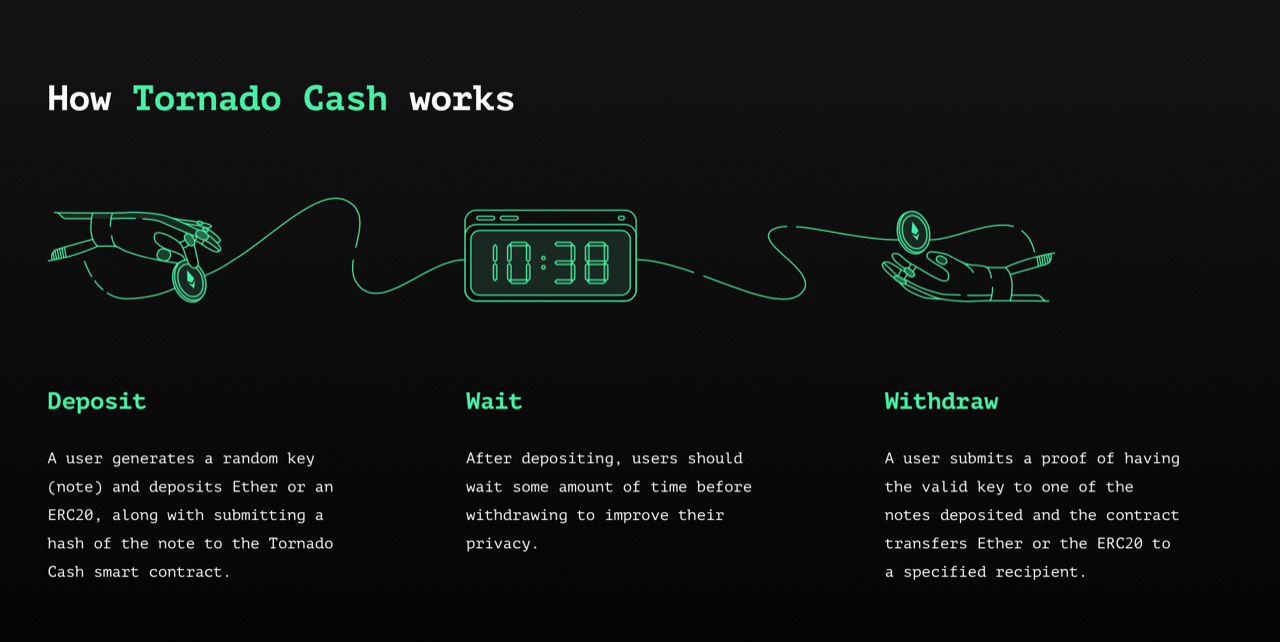
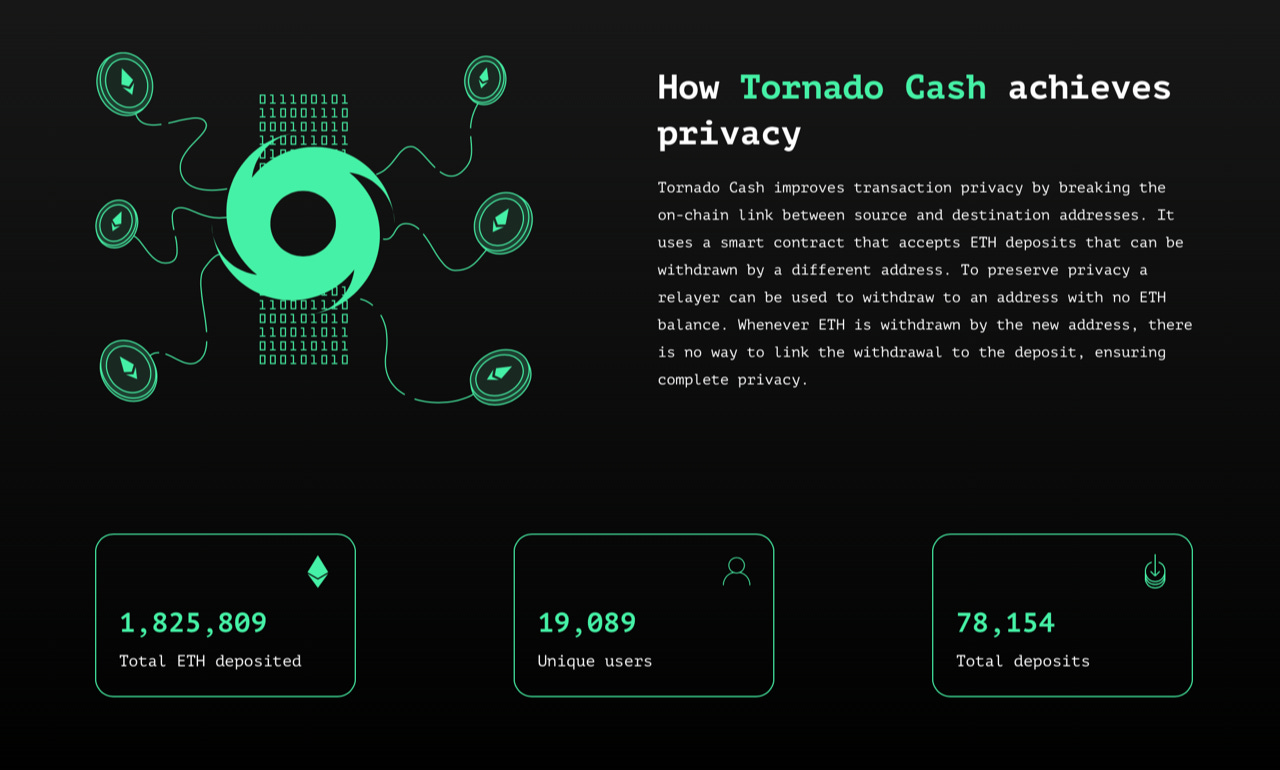
Let’s begin by having a closer look at Tornado Cash. What is it? It is a cleverly designed decentralized protocol for making transactions on Ethereum private. Let’s say you are in possession of some Ether you’d like to launder, err, move to another wallet with complete privacy. You deposit your Ether with Tornado Cash and the protocol generates a randomized key known only to you. You can then use that key to withdraw the Ether you originally deposited into another wallet at your leisure and, because there’s no way to ever connect the two, you’ve effectively cleaned the Ether from any ties to your original wallet.
In case it wasn’t obvious enough, the website contains a handy diagram for you. Dirty money on the left, clean money on the right. Presto! Most amazing to me is Tornado Cash claims to have laundered, err, anonymized 1.8 million ether. That’s as much as $5 billion in notional value, depending on the average price of Ether you choose. It’s a big number! As a reminder, like I’ve said before on this Substack, if I try to withdraw $9,999 of my own cash from a bank, lawfully earned and dutifully reported to the IRS, I’ll likely be charged with structuring. Meanwhile, billions are being structured in plain sight. This is why I write about crypto. The discrepancy in enforcement is literally unbelievable.
At least it was.
My journey down the mixer rabbit hole led me to Bitcoin Fog. In April of 2021, the Department of Justice (DOJ) announced it had identified and charged the founder of the bitcoin mixer with several felonies. Here’s how Wired described it:
“US authorities on Tuesday arrested Roman Sterlingov in Los Angeles, according to court records, and charged him with laundering more than 1.2 million bitcoins—worth $336 million at the times of the payments—over the 10 years that he allegedly ran Bitcoin Fog. According to the IRS criminal investigations division, Sterlingov, a citizen of Russia and Sweden, allowed users to blend their transactions with those of others to prevent anyone examining the Bitcoin blockchain from tracing any individual's payments. He took commissions on those transactions of 2 to 2.5 percent. In total, the IRS calculates, Sterlingov allegedly took home roughly $8 million worth of bitcoin through the service, based on exchange rates at the times of each transaction.”
The importance of this arrest cannot be overstated. First, the amazing manner in which the DOJ was able to deduce Sterlingov’s identity shows they have excellent crypto sleuthing capabilities and are willing to use them. Second, and most pertinent to this piece, the DOJ is claiming incredibly expansive jurisdiction in this case. Here’s how it was described in an article on Lexology’s website – an outstanding resource for international legal updates and critical analysis (emphasis added):
“The DOJ’s conception of its jurisdiction is extremely expansive. While there is no doubt additional evidence against Sterlingov that was left out of the IRS affidavit, the only alleged tie between Sterlingov and the US is that the Bitcoin Fog website was accessible by users within the US, and that Bitcoin Fog processed at least one transaction for a user based in DC (the undercover agent).”
The article continues (once again, emphasis added):
“The DOJ has taken a dim view of crypto mixers. Although the cases against Harmon and Sterlingov both relied on the defendants’ alleged cooperation with illegal Darknet marketplaces, the DOJ’s public stance on mixers raises the possibility that any service which acts to conceal transactions on the blockchain for any reason are potentially in the crosshairs of US law enforcement.”
A key charge against Sterlingov is especially dangerous. An undercover agent used Bitcoin Fog from a computer in the US in an attempt to anonymize some bitcoin. The agent sent an email to Bitcoin Fog seeking instructions while casually stating that their bitcoins were obtained illicitly. The email was never responded to or acknowledged, but the agent was able to anonymize their holdings anyway. The fact that Bitcoin Fog didn’t prevent it was criminal enough for the DOJ. Putting aside the potential entrapment issues here, it was more than enough for the DOJ to press charges. It’s called know your customer for a reason, I guess.
There are several high-profile crypto exchanges that technically “don’t operate” in the US, but these restrictions are regularly circumvented by the use of VPN software. Is it much of a stretch to assume a scenario where an undercover agent logs on, creates and funds accounts from US soil, sends a few emails, and when those accounts aren’t shutdown charges are filed against the operators of these exchanges? I certainly don’t think so. Certainly not after reading the Sterlingov case.
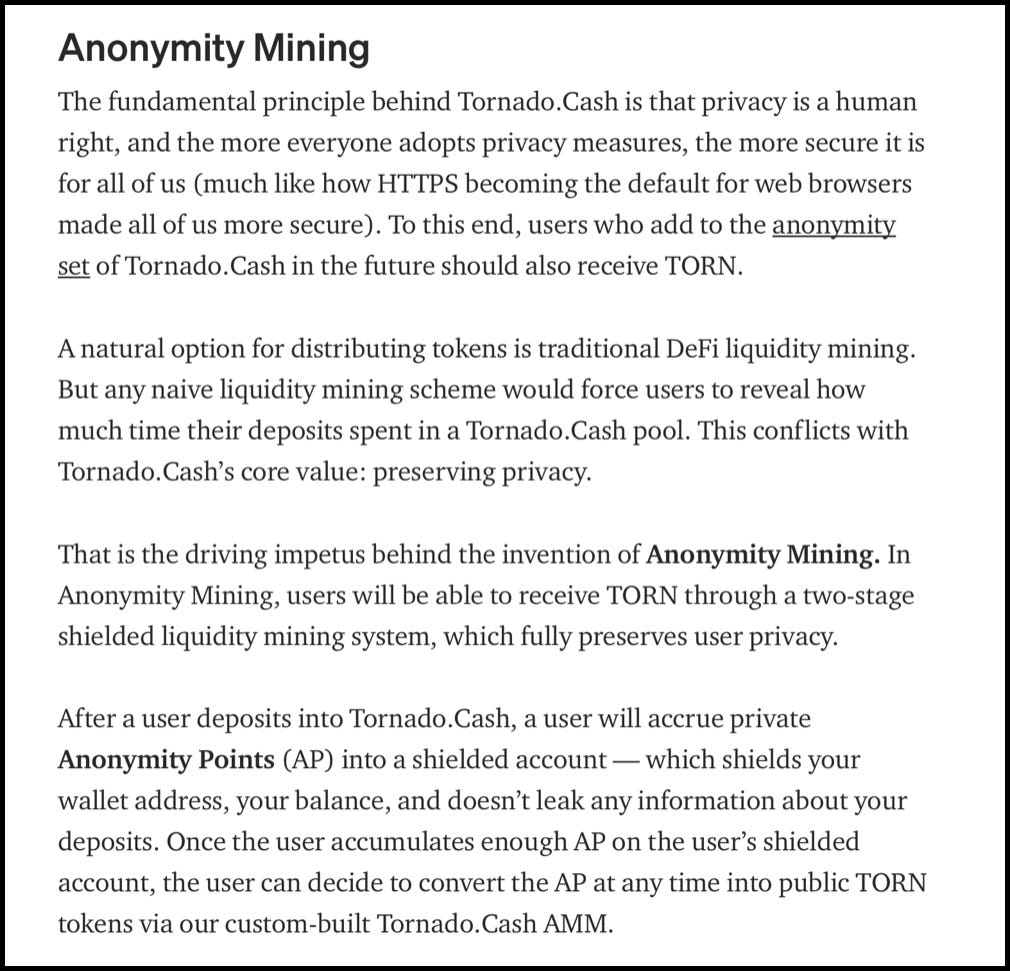
Here’s another thought experiment. Mixers require a certain critical mass of users to truly anonymize. These mixers often incentivize people to participate. For example, Tornado Cash offers Anonymity Mining. People can earn TORN tokens by depositing Ether and then jumping through a few more hoops. Is it a stretch to assume that the DOJ decides that all mixers predominately exist to launder money and anybody who participates whatsoever can be charged with conspiracy to facilitate laundering? Does ownership of TORN itself make you susceptible to such charges? Does listing TORN on an exchange?
You might think I’m just being a paranoid chicken – and you’d be at least half right. But I submit that the DOJ believes it has essentially unlimited jurisdiction when it comes to crypto. You might not like it – it might even be one of the main reasons you are passionate about crypto to begin with – but to ignore it seems like a serious mistake.
If you enjoy Doomberg, subscribe and share a link with your most paranoid friend!





"the US dollar is a giant Ponzi scheme, Wall Street is totally corrupt and exists to enrich the top 1%, the big banks launder billions of fiat currency per year for all manner of unseemly characters, and our politicians are nothing more than a mob family with unjustified power to police us. To which I say I totally agree!!!"
i assume it's an irony i don't get. neither do i get how come "I’m not personally pro- or anti-crypto per se" given your previous post on a drunken saylor... maybe i lack a healthy dose of humor today?
Want privacy = laundering money? Governments = God? More than a few governments were disappeared when the firearm became privatized.
The law says you must pay 99% of your income to the government. You will comply, of course, without question or complaint?